Barracuda Email Gateway Breach: 5 Things To Know
The attacks exploited a ‘critical’ vulnerability in the company’s on-premises Email Security Gateway that has now been patched.
Barracuda Customers Breached
While cybersecurity vendors are in business to protect organizations against hackers, sometimes the products that are supposed to do the protecting end up becoming the means utilized in a breach. One of the most widely felt cyberattack campaigns of 2023, for instance, was the series of attacks that leveraged a vulnerability in Fortra’s secure managed file transfer product, GoAnywhere.
[Related: Fortra: Certain On-Prem Customers Were Targeted In GoAnywhere Attacks]
Now, cybersecurity industry stalwart Barracuda has disclosed that it, too, has seen a product fall victim to an attack leveraging a zero-day vulnerability. The vulnerability in Barracuda’s Email Security Gateway appliance used by on-premises customers has now been patched, but not before an unspecified number of customers were breached. The breach was revealed by the Campbell, Calif.-based company on Tuesday, and as of this writing, further details have not been provided by the company beyond the initial disclosure. More details about the vulnerability itself, however, did appear online Wednesday, including that Google — in its capacity as a vulnerability numbering authority — has given a “critical” severity rating to the flaw in the Barracuda email security appliance.
What follows are five key things to know about the Barracuda Email Security Gateway breach.

Full Impact Is Unknown
In its post disclosing the breach Tuesday, Barracuda said that some Email Security Gateway customers were impacted by a breach last week that exploited a zero-day vulnerability in the appliance. The cybersecurity vendor didn’t specify in the post how many customers were affected, and said in an email to CRN that it’s not sharing further details on that aspect at this point.
Barracuda said in the post that the vulnerability was discovered on May 19, and the company deployed a patch “to all ESG appliances worldwide” the following day. A second patch was deployed on May 21 to all Email Security Gateway appliances.
The investigation so far has found that the vulnerability “resulted in unauthorized access to a subset of email gateway appliances.” Affected customers have been notified, Barracuda said.
“If a customer has not received notice from us via the ESG user interface, we have no reason to believe their environment has been impacted at this time and there are no actions for the customer to take,” Barracuda said in an email to CRN Wednesday.

Only On-Prem Customers Affected
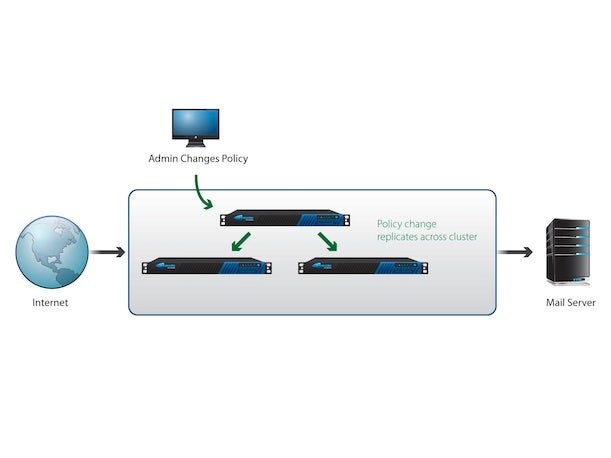
Barracuda’s Email Security Gateway is a product used by on-premises customers for filtering of all email traffic, both inbound and outbound. The appliance, which is cloud-connected, is often used to protect Microsoft Exchange environments. In addition to email filtering, the Email Security Gateway provides on-prem customers with data loss prevention, antivirus, encryption and DDoS protection, according to a page of Barracuda’s website.
Barracuda noted that its investigation has been “limited to the ESG product, and not the customer’s specific environment.” As a result, “impacted customers should review their environments and determine any additional actions they want to take,” Barracuda said in its post.
Other Barracuda products were not affected by the zero-day vulnerability, including the company’s SaaS email security services, Barracuda said in its post.
As customers have shifted to the cloud over the years, the company has been increasingly focused on moving customers to its Barracuda Email Protection offering, which secures organizations that use the Microsoft 365 cloud email and productivity suite.

‘Critical’ Vulnerability
While the zero-day vulnerability in Barracuda’s Email Security Gateway appliance has now been patched, more details emerged Wednesday about the seriousness of the security flaw. Barracuda had provided few specifics about the zero day vulnerability, which is tracked at CVE-2023-2868, other than to say that it had affected a module used for initial screening of attachments for incoming emails. (CVE refers to the Common Vulnerabilities and Exposures system used for tracking known security flaws.)
On Wednesday, an entry went live on the National Vulnerability Database website about the flaw, showing that the Barracuda ESG vulnerability has been given a severity score of 9.4 out of 10.0 by Google. The assessment of the vulnerability was conducted by Google in its capacity as a CVE numbering authority, or CNA.
According to the entry, the issue consisted of a “remote command injection vulnerability” that affected versions 5.1.3.001 to 9.2.0.006 of the Barracuda appliance. From the entry: “The vulnerability arises out of a failure to comprehensively sanitize the processing of .tar file (tape archives). The vulnerability stems from incomplete input validation of a user-supplied .tar file as it pertains to the names of the files contained within the archive. As a consequence, a remote attacker can specifically format these file names in a particular manner that will result in remotely executing a system command through Perl’s qx operator with the privileges of the Email Security Gateway product.”
Barracuda told CRN in an email Wednesday that it’s currently not providing details about who discovered the vulnerability initially.
On-Prem Systems: A Popular Target
Barracuda’s Email Security Gateway appliance was first introduced by the company in 2003 — originally as the Barracuda Spam Firewall — and it has become just the latest on-premises product to be targeted by attackers.
Microsoft Exchange environments — which the Barracuda appliance is often enlisted to protect — have themselves been among the most popular targets for attackers in recent years, thanks in part to a series of critical vulnerabilities in the systems.
The December ransomware attack against the Rackspace Hosted Exchange service, for instance, was enabled by a zero day exploit associated with an Exchange vulnerability (CVE-2022-41080). The attack saw hackers gain access to dozens of accounts, while tens of thousands lost access to their historical emails in the wake of the attack.
In September 2022, the latest remote code execution vulnerability in Exchange, known as “ProxyNotShell” (CVE-2022-41082), was disclosed by researchers. Prior critical Exchange vulnerabilities have included the four widely exploited bugs that were revealed in early 2021 as well as the ProxyShell vulnerability, disclosed in August 2021.
More recently, in the Fortra GoAnywhere attacks, the cybersecurity and business software vendor said that certain customers with on-premises deployments of the file transfer platform were “at an increased risk” from the attacks. The GoAnywhere vulnerability “was used against a small number of on-premise implementations running a specific configuration of the GoAnywhere MFT solution,” the company said in an April blog post. This occurred as far back as Jan. 18, Fortra said.

Hatem Naguib
The Cloud Alternative
For Barracuda, a major source of growth has been around helping customers to transition to Microsoft 365 cloud-based email, CEO Hatem Naguib told CRN in a March interview. “We’ve been very successful at protecting our customers as they migrate to cloud. And for many of our customers, their first migration is the Office 365 journey,” he said.
“We’ve been providing them the security [including] what we used to do in the old email gateway — when your email comes in, we’ll check it and [determine if] it’s a good email or a bad email. But now there’s a far more sophisticated set of security tools that leverages all of the components around where your data is sitting, who’s sending you what emails, at what time,” Naguib told CRN in March. “We’ve leveraged extensively, for a long period of time, machine learning and AI capabilities to help predict when customers were going to get [business email compromise] attacks … And more and more of our customers continue to adopt the solutions to prevent account takeover and the type of phishing attacks that they’re seeing. But also the ransomware, which is just completely dominating the small to medium enterprises.”
Ultimately, the company’s cloud email security platform “for us continues to expand and grow,” he said. “And it’s not just email now — it’s all collaboration. And it continues to be a really key component for what we drive for our customers.”